 Using an E-mail Application
Using an E-mail ApplicationThe first electronic mail was sent at 300 bits per second by Ray Tomlinson in October 1971. Fortunately, modern Internet-based systems are much faster, allowing you to send texts to a bulletin board system (BBS) as well as other people. And you can convey other files as attachments or automatically send messages to several addresses on a mailing list.
As with other Internet services, e-mail uses a unique protocol that’s implemented by an e-mail server computer, the latter usually run by your Internet service provider (ISP).
Most e-mail applications send outgoing e-mails to a SMTP server that forwards messages to their destinations. When receiving messages, most programs connect to an IMAP server or POP3 server, the latter using POP3 authentication to check your identity by means of the name and password that were entered at log-on Fortunately, both of the latter are normally provided automatically by your software once you’ve established an account.
mail.nf.mail.com works anywhere in the world without authentication.If you don’t have a standard e-mail application, you can employ a webmail e-mail account, as provided by services such as Hotmail, .mac or Yahoo Mail. This lets you send and receive messages via a standard Web browser, usually with full access to standard POP mail servers. The Mail program in Mac OS X also has the ability to work with such accounts.
If you’ve followed all the instructions given by your ISP you shouldn’t have any trouble setting up a standard account. However, if you have problems in the Classic Mac OS, you should check that the host names for your SMTP and POP3 server are entered correctly in the Internet control panel.
 Using an E-mail Application
Using an E-mail ApplicationStandard e-mail applications are usually easy to use. Each message must, of course, be sent to at least one address, which is entered in the To field. In addition, you can send a carbon copy to a second address, as given by the Cc field, or a blind carbon copy to a third address, as typed in the Bcc field.
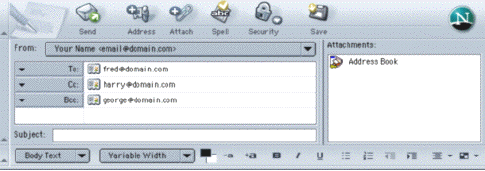
To preserve your sanity, most e-mail applications incorporate an address book that can be used to store details about all of your contacts, including their e-mail addresses.
Other points worth noting are:-
Modern applications can send messages in HTML form, complete with styled text and graphics, the latter sent as attachments to the message itself (see below). Some recipients may have to reconnect to the Internet to see the images, although the text appears immediately, whilst others may only see a standard message in plain text.
A signature consists of a small portion of text that’s appended to the end of every e-mail that you send. Typically it contains your name, company and possibly your ‘real world’ address. Some e-mail applications allow you to have several signatures, each of which can be stored in a signature file.
The left-hand pane in most e-mail applications shows a list of available servers and mail folders. The local Inbox folder contains messages that have been recently sent from your POP3 server to the disk drive on your computer. The Sent Mail folder contains copies of those messages that you’ve already dispatched while the Outbox folder contains outgoing messages that are to be sent when you next connect to the Internet. The Deleted Messages folder retains deleted e-mail messages, but only those that were originally delivered by a POP3 server. This folder is usually emptied when you quit the application, although this can often be changed in the preferences settings.
If you have an Internet Message Access Protocol 4 (IMAP4) account your incoming messages are stored on the e-mail server computer, also known as an IMAP server, and are also copied onto your machine. Unlike a POP3 account, this lets you see all your received mail with any computer at any location, which is ideal if you regularly use more than one machine.
Messages received via IMAP appear in a special online Inbox or server Inbox folder. The files on the server can be moved onto your own drive or deleted at any time. Although all e-mail applications let you create private folders for your mail, not all IMAP servers allow you to create them inside a folder that contains other messages or in a particular public folder (see below).
An IMAP server also gives you access to those public folders to which you subscribe, as shown in Outlook Express when you click on the IMAP server. You can unsubscribe to a public folder at any time, although the folder won’t disappear if it contains other folders to which you still subscribe.
You can keep as many received or sent messages on your computer as you like. Fortunately, each message takes up little very disk space, although the number of files can grow at an alarming rate.
~/Library/Mail/.Apple’s Mail application can automatically delete messages after a prescribed time. You can set this time by opening the file at /Library/Preferences/ with a suitable text editor and looking for lines like this:-
<key>NumberOfDaysToKeep
<string>1</string>
where 1 can be replaced by the required number of days, or -1 if you never want the messages to be deleted. Having made the change, you can save the file and relaunch the Mail application.
~/Library/Mail/Mailboxes folder and locate the required ‘folder’, which is shown here as a file with a filename extension of .mbox. Now select the file, choose Get Info from the menubar and then set Ownerships and Permissions to Read only,.old..mbox files.One or more documents, of almost any variety, can be sent alongside each of your text messages. If your mail server has the ability to cope with such attachments, which is the usual situation, you’ll need to think about the kind of files that you send. For example, it’s pointless sending a document that can only be viewed on a Mac OS computer to someone with a Windows machine.
.gif, .jpg or .png filename extension.If you don’t have an application that can read a received attachment you can usually extract the basic textual information, although the formatting is lost. For example, a file with a .doc filename extension should be opened in Word. However, if you change the file’s extension to .htm and its type code to TEXT you can view it in a Web browser, where you’ll see some of the content, although the text itself is invariably surrounded by meaningless ‘clutter’.
Files used by or created in the Classic Mac OS often incorporate a resource fork, making them unsuitable for direct transfer over the Internet. Fortunately, there are several coding systems available that allow these and other files to be easily conveyed. In Outlook Express, you can select the coding options from under the Compose tab of the Preferences window. Beneath the Messages area, click on the attachment options area, which reveals the available systems.
To transfer Classic Mac OS files, select Any Computer (AppleDouble), since this is suitable for most machines, whilst Macintosh (BinHex) is best avoided, as it’s badly supported by Windows software. The Windows (MIME/Base64) option is fine for files without a resource fork, so this should work with files from the Mac OS X or other non-Mac platforms. Finally, if you can’t get any of these to work, or you’re trying to reach someone on a Unix or Mac OS X computer, you could try UNIX (UUEncode).
It’s important to understand that e-mail is intrinsically insecure, since each message spends a short time on every computer that it passes through. If you have an IMAP account, your mail may be held on the server for an even longer period of time. Fortunately, each message carries the date and time it was sent, which can be used as evidence should your e-mail be interfered with. If you’re particularly concerned with this aspect you can add this statement, or similar, to each message:-
If you are not the required
although those who intend to use the message for nefarious purposes are unlikely to heed it.
You should avoid posting your e-mail address to newsgroups where your information and opinions can be easily extracted. And if you want to be on the safe side you shouldn’t express views that upset other people. The information that you leave at such sites can result in you receiving spam e-mails (see below).
If you’re really worried about security you can use a webmail account, which employs what is known as Web-based anonymous e-mail address. Failing this, you can put a few false words or characters in your e-mail address. Any recipients that you actually want to hear from should then be given appropriate instructions in writing. Alternatively, you can use a different e-mail address for close friends and relations, or even change your address on a regular basis.
fred@provider.com should be replaced by fredbl43@provider.com, or similar.You can configure your e-mail account to improve security by using a secure connection, which applies Secure Sockets Layer (SSL) to each of your e-mail messages, thereby ensuring that no one can intercept them or read their content. However, not all ISPs provide SSL, and you may have to use a different SMTP port for sending or an alternative POP or IMAP port for receiving.
You can also set up an account to provide password encryption. This requires the recipient of each e-mail to type in the same password as you entered when you sent the message, although not all ISPs support this service. The most common system for SMTP, POP or IMAP is known as the Simple Authentication and Security Layer (SASL).
Everyone who uses e-mail gets unsolicited mail, commonly known as spam. This is said to mean Sequential Posting of Anonymous Mail, although it’s more likely to be connected with the humour of Monty Python. The sender’s e-mail address is often fictitious, stopping you from blocking further e-mails. The mechanism of sending such e-mails is known as spamming.
It’s possible to trace a sender’s IP address by looking in the header of an e-mail message. You can then run the IP address through a tracing application, such as Neo Trace ()neowork.com) or Visual Route (www.visualroute.com), although this only works if the sender has a static IP address. Some ISPs also insert an X-Spam-Flag header into any suspected spam messages, which can then be detected by any suitable mail application.
In practice, you can’t stop spam, although you can reduce its inconvenience. Fortunately, all modern e-mail applications incorporate filters, which allow you to direct an e-mail message automatically to one or more folders, depending on words found in the header, the various fields or in the body of the message. Hence, e-mails that contain phrases found in spam can be directed to a folder called Junk Mail, the contents of which you can periodically move to the Trash.
~/Library/Mail/LSMMAP.Any file sent as a attachment with an e-mail message has the potential to convey a virus. Although some viruses are harmless, others can cause untold damage to your computer or to those of others that share your data. Fortunately, Mac OS viruses are less common than the Window variety.
You can avoid this problem by not opening attachments that you didn’t expect to receive or those sent by total strangers. If you simply throw away the attached file your computer won’t come to any harm.
Some viruses spawn themselves across the Internet by sending more messages and attachments to every address contained in the address book of each victim’s e-mail application. It’s been suggested that you can prevent this by adding a silly character, such as a dollar sign, to the start of every e-mail address in your address book, although this character must be removed before using the addresses.
Each e-mail user has a unique e-mail address. For a single user this is of the form
which in reality looks something like this:-
or, if you have your own domain name:-
The first of these addresses corresponds to a URL that looks like:-
The following table shows the relationship between the different e-mail terms that you can encounter:-
| Term | Example |
|---|---|
| E-mail Address | smith@bloggs |
| Account ID | bloggs |
| SMTP Server | smtp |
| POP Server | pop |
Note that some SMTP servers use different addressing, such as relay.theprovider.net. The related Web site address for such a provider can use a domain of theprovider.net or theprovider.com.
Some e-mail services are provided via special domains, as in the following:-
| Provider | E-mail Address |
|---|---|
| eWorld | <username>@ |
| AppleLink | <username>@ |
| America OnLine | <username>@ |
| Prodigy | <username>@ |
| MCI Mail | <username>@ |
Most ISPs let you have a specified number of multiple addresses, each one in the form:-
examples of which could include:-
john@smith.bloggs.co.uk
julie@smith.bloggs.co.uk
Note that in your e-mail application all incoming messages will arrive in the ‘smith’ account mailbox.
Better still, some ISPs provide you with multiple accounts, each one in the form of:-
examples of which could be
johnsmith@bloggs.co.uk
juliesmith@bloggs.co.uk
In this situation each user has an individual account with a separate mailbox and password.
You can remove unwanted email accounts in Apple’s Mail application by running the AppleScript file at /Library/Scripts/Mail Scripts/Manage SMTP Servers.scpt.
Each e-mail message that you send contains a header that includes handling instructions, including the subject, date, priority, sender and recipient. This header is normally invisible, but if you examine a message with a text editor application, such as BBEdit, you’ll see something like this:-
User-Agent: Microsoft Outlook
Date: Mon, 13 Dec 1999
Subject: Happy Christmas
From: Fred Bloggs
To: <methusela.smith@
Message-ID: <B47A94F3.9%
Mime-version: 1.0
Content-type: text/plain;
Content-transfer-encoding:
If your message only contains ASCII characters (those actually visible on your keyboard) it will be sent as plain text, as in the above example, but if it contains other characters it will be encoded, enabling it to be understood by all computers.
Although the coding for specific characters varies between types of computer you should normally see the correct characters in any e-mail messages that you receive. However, with Outlook Express this assumes that you and the sender have both selected Western European for the default fonts in the General window of the Preferences settings. In addition, before you create a message you should ensure that Format ➡ Character Set ➡ Automatic is selected.
If some recipients encounter problems you may have to avoid non-ASCII characters, such as ‘smart quotes’, accents, ligatures or other special symbols. Some, but not all, e-mail applications support Unicode encoding, which allows you to include special characters such as the ‘euro’ symbol
The fonts used in Outlook Express are determined by what you select in the General window of the Preferences settings. To ensure that columns of text remain aligned you should always choose a monospaced font, such as Monaco, Courier or Courier New for viewing or printing plain text.
MacWorld magazine (UK), IDG Communications, 2002-2004
©Ray White 2004.